Blog
Top 10 Privileged Access Management Tools in 2026
The top 10 privileged access management tools in 2026, compared by features, deployment model, pricing, and use case. Includes open-source options, enterprise PAM platforms, and cloud-native solutions to help security teams choose the right fit.
Published on 2026-04-21
SSH Key Management: Best Practices for Enterprise Security in 2026
Learn how to manage SSH keys securely at scale. Discover enterprise SSH key management best practices, common risks, and how JumpServer automates privileged access control.
Published on 2026-04-16
RBAC in Privileged Access Management: A Practical Implementation Guide
Role-Based Access Control (RBAC) is the security model that puts least privilege into practice inside a PAM solution. This guide walks IT and security teams through how RBAC works, how to implement it, and how to avoid the mistakes that leave privileged accounts exposed.
Published on 2026-04-10
What Is Privileged Identity Management (PIM)? The Complete Guide for IT Teams
Privileged identity management (PIM) secures elevated accounts that hold the keys to your most critical systems. This complete guide covers what PIM is, how it differs from PAM and IAM, best practices for 2026, and how to implement it with open-source tools.
Published on 2026-04-01
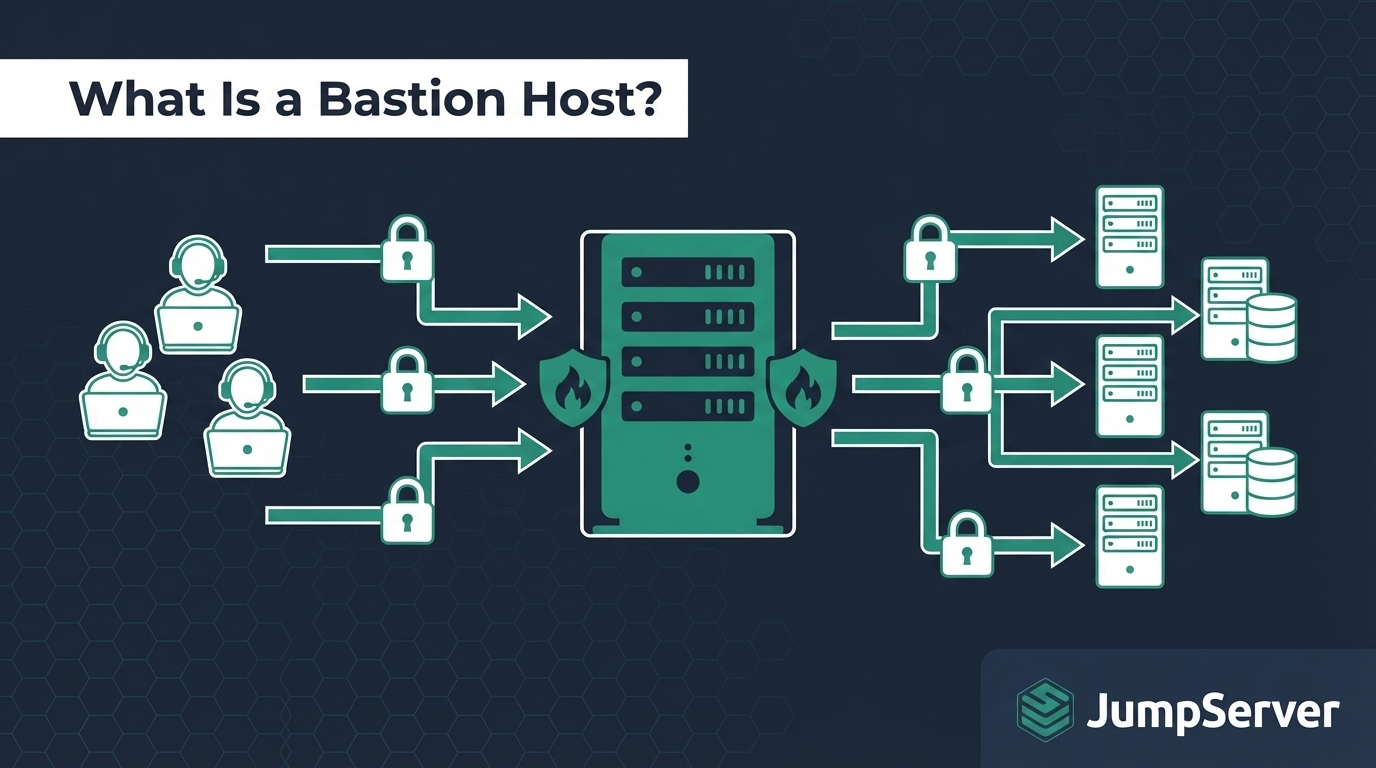
What Is a Bastion Host? Architecture, Security Best Practices, and Complete Setup Guide
Learn what a bastion host is, how it works, its network architecture, and how to secure one with best practices. Includes a JumpServer step-by-step setup guide.
Published on 2026-03-06